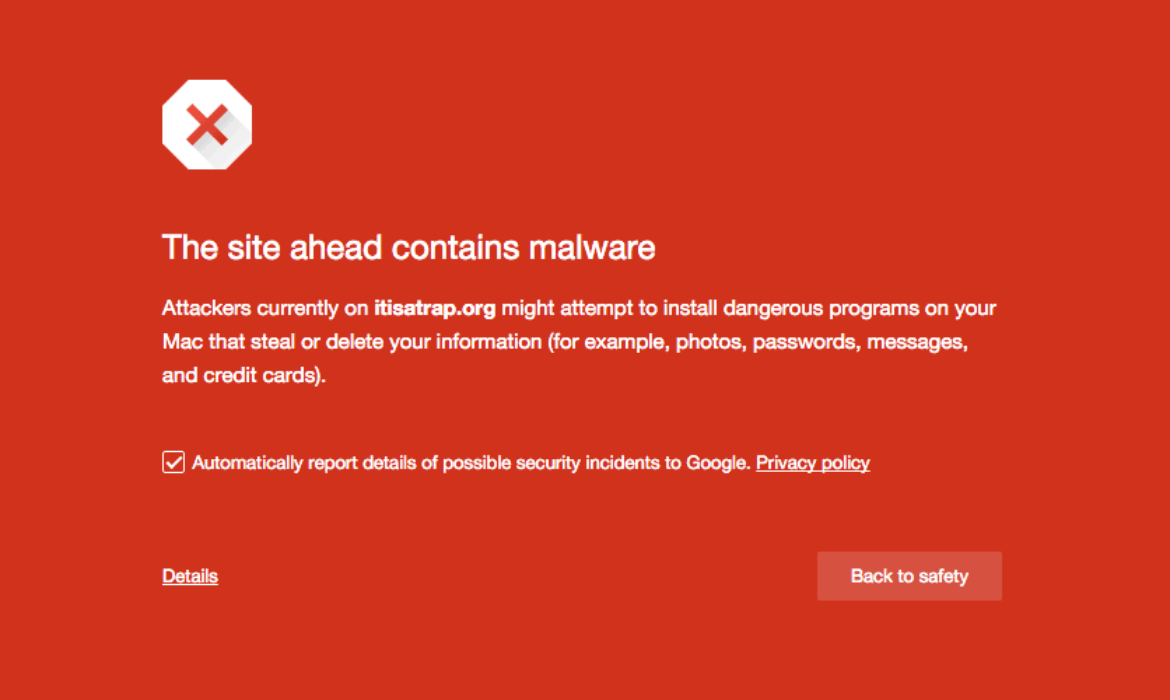
So, did it hurt? When you landed at the bottom of the SERPs, I mean, and Google slapped a scary red warning message on your site telling people to keep out.
If this happened due to an error on your part (bad SEO, shady linking tactics, etc) that’s one thing.
But if your site was hacked and now contains malicious code, that’s just adding insult to injury – and can really damage your reputation.
Unfortunately, that’s just one of the risks of being in charge of your own site maintenance. Stuff like this can happen.
Sure, it’s fantastic to build your own site in WordPress, but as Spiderman says, with great power comes great responsibility.
To put it plainly, you have control over how your site looks, but you’re also in control when/if your site runs into problems.
If you’re hacked, you will probably get blocklisted by Google. Period. Google isn’t going to take any chances with its reputation.
So, if your site smells even the slightest bit fishy, the search engine is going to blocklist you, knock you from your spot in the rankings that you’ve worked so hard for, send your site plummeting in the SERPs and tell anyone who lands on your site to stay away because it’s dangerous.
And that’s a real bummer. But the key is knowing what to do next.
Should you find yourself on Google’s Blocklist (or you’re a bit fuzzy on what the blocklist even is), we’ve put together a comprehensive step-by-step guide to getting it handled ASAP.
(Click here to go straight to the step-by-step-guide)

Google Blocklist: A Definition
A website that has been blocklisted by Google will generally experience a dramatic drop in organic search traffic.
It’s sudden and huge, and when your Analytics graph inverts sharply, it’s usually the biggest clue to a webmaster that something bad has happened.
How Did I Get on the Blocklist?
There are several ways your site might’ve got on the blocklist. But generally speaking, when a search engine finds suspicious code or activity on your site that its internal algorithms determine to be malware, it will remove the site from search results immediately.
Instead of risking the integrity of the search results and their safety for users, removing the questionable site is the least resource-intensive action the search engine can take.
Now, what is malware exactly?
In this case, it can be anything that Google deems suspicious, including phishing schemes, hacks, information or email address scrapers, trojan horses, and more.
The sad thing here is that you won’t even know your site has been hacked the vast majority of the time until your organic search traffic falls off a cliff.
In some cases, however, there will be tell-tale signs that something is amiss.
This can either come in the form of suspicious things you come across yourself or through warnings, shutdowns, or other actions taken by external sources.
Of course, there are occasions where the webmaster is responsible for the blocklisting.
Things you should never do if you want to avoid the blocklist include:
- Violating Copyright or DMCA Claims: Stealing content is frowned upon by the world. Don’t do it.
- Keyword Masking: Hiding keywords by making the text the same color as the site’s background is so 1998. If Google finds out, you’ll be de-indexed quick.
- Linking to Spammy Sites: Be mindful of where you link to. It should be a priority of yours to link only to high-quality sites.
However, a lot of the time, hackers will implement these link baiting and keyword spam schemes as a part of infecting your site with malware.
Regardless of whodunnit, however, Google will treat affected sites the same way: with a swift and thorough blocklisting.
What Does Blocklisting Look Like?
Blocklisting is fairly obvious when it happens.
Your analytics will take a nosedive, as I mentioned above. Or, if you do a simple Google search for “site:yoursitehere.com” and no results are found (assuming your site has already been indexed), chances are really good that your site has been blocklisted. This is one of the manual ways to check for blocklisting.
Another way to check for blocklisting is to regularly access and review data in Google Search Console.
This makes it easy for you to see what sites link to you, what search queries you’re ranked for, 404s, server errors, and overall site health.
Any funny business happening with your site is likely to show up here before your site is blocklisted, so keeping a watchful eye is really important when attempting to maintain the integrity of your site.
Security plugins can also be a great tool to help determine if your site has been hacked and/or blocklisted.
A Plugin to the Rescue

When it comes to a plugin, our very own answer to security, Defender, can stop brute force attacks, SQL injections, cross-site scripting XSS, and more vulnerabilities that will prevent you from getting hacked and blocklisted in the first place.
Defender can also scan your site and track down malicious code. If there’s malicious code detected, Defender shows you exactly what it is and the locations. You can then delete it in one click.
Be sure to read our article about stopping hackers in their tracks, so you don’t even have to worry about getting blocklisted by Google to begin with and try Defender out for yourself for free.
Security Warnings & Diagnostics: A Primer
So, we’ve already talked about preventative measures and the ways you can check to see if your site has been blocklisted, but I feel like it’s a good idea to spend additional time talking about what some refer to as the “symptoms” of being blocklisted.
Not every blocklisted site will exhibit these features, but this is a good rundown of what to look for:
- There is sudden traffic to your site for keywords that have nothing to do with your site’s content—particularly related to pharmaceuticals.
- Your site suddenly redirects to another site not in your possession.
- New administrators or users appear in your site’s dashboard that wasn’t created by you or anyone with authorized admin access.
- Your site is suddenly flagged as potentially containing malware in search engine results and by desktop or mobile anti-virus detection software.
- Your web host shuts down your site.
It’s important to note the various security warnings Google can provide as well. While these aren’t technically blocklisting, they can sometimes indicate your site is well on its way to being blocklisted.
Should you be fortunate enough to catch suspicious activity thanks to a security warning, you may be able to sidestep the headache of being blocklisted altogether.
These warnings appear on the search engine result page where your site is listed. They can also take a couple of different forms. Here are two of the most common warnings you’ll come across:
This site may harm your computer
This warning occurs when Google believes your site contains a Trojan or other piece of code that triggers a download prompt that is malicious.
Those fake anti-virus pop-ups and automatic file downloads are the most common examples of what Google is referring to when it displays this warning.

This site may be hacked
This gets to the point, doesn’t it? This warning displays when Google has reason to believe your site has been completely hacked and taken over by someone other than you.
The sudden appearance of content that doesn’t belong with the rest of your site, bank directories, and other red flags trigger this warning.

Other Blocklists
While this article focuses on getting off Google’s blocklist, it’s worth noting there are other blocklists that may pick up on malicious content or security threats on your site.
These are some of the main blocklists:
- Norton Safe Web
- Phish Tank
- Opera
- SiteAdvisor McAfee
- Yandex (via Sophos)
- ESET
If Google reports your site as clean, it is still possible for Opera (the browser, that is) or even Yandex (the search engine) to blocklist your site.
So if you do notice a drop in SERPs or security warnings displaying in browsers other than Chrome, it’s a good idea to check these other blocklists to see if your site has been compromised.
A Step-by-Step Guide for Getting off the Google Blocklist
Now that you’re all clear on what blocklisting is, how to tell if it’s happened, and what the warning signs are that you might be headed for the blocklist, we can start discussing how to get your site off it for good.
Step 1: Check if you’re blocklisted
Should go without saying, but you need to be 100% sure if your site has been blocklisted before you move forward.
- Check your site’s status to determine safe browsing. Just input your site’s URL and review the results.
- Use Google Search Console’s URL inspection tool to see what Googlebot sees when accessing your site.
Step 2: Locate the Suspicious Code
There are many different places you can look on your site to find malware.
As mentioned before, the simplest way of finding malware is with a resource like our Defender plugin.
If you’re not using a plugin like Defender, it’s not always so easy and scanning through the code on each page, however, sometimes the culprit is embedded in your server somewhere.
Still, there are a few places that hackers target more than others. You will need FTP access to get to some of these areas to start cleaning up the mess.
If your site is suddenly redirecting to another site, you should check the following areas for suspicious code:
- Core WordPress files
- Your site’s index (check both .php and .html!)
- .htaccess
If your site is now triggering downloads for visitors, check out the following spots:
- Header
- Footer
- Index (check both .php and HTML)
- Your theme’s files
If you’re suddenly seeing a bunch of Pharma information on your site and believe it’s been compromised by a phishing campaign, check:
- Any HTML file
- Index .php and .html
- For the appearance of new directories you didn’t create
You can also leverage the Google Diagnostic Page to figure out specifically what part of your site has been compromised. Is it just one page? One directory? Or the whole site?
Keep reading through the results to see when Google last visited your site.
This is referred to as the “scan date.” Also, take note of when Google found malware or suspicious content. This is referred to as the “discovery date.”
Now, if you’ve tried to fix your site after the last “scan date,” Google doesn’t know about it yet. Patience is a requirement when getting your site off the blocklist, unfortunately.
You can bring Google’s attention to your attempts to fix the issues, but we’ll talk more about that later.
Note: Sometimes, Google Search Console will show that certain HTML pages of your site have been infected, but this isn’t necessarily the case. When dealing with WordPress, likely, the core file responsible for generating the HTML file in question is infected.
Step 3: Dig Deeper: Pretend You’re a Bot or User Agent
Sometimes running tests to see if your site (or a client’s) is infected would put your own computer at risk.
You couldn’t just open up your web browser and load the site directly without putting your machine in danger.
So, to bypass this, you can use cURL in the command-line interface (CLI) to basically pretend you are a Google bot or a user agent.
For example, you would input the following to emulate a bot:
$ curl –location -D – -A “Googlebot” somesite.com
Once you input this, you’re going to want to look for anything that doesn’t make sense in the code.
So, bits that are in a different language than your own or content that looks like total gibberish.
Yes, you’ll need to understand HTML, at the very least, here. Anything in an iframe or script tag should get your careful attention, too.
You can also use this bit of code to emulate a user-agent:
$ curl -A “Mozilla/5.0 (compatible; MSIE 7.01; Windows NT 5.0)” http://www.somesite.com
You can swap out what browser is referenced here depending on your needs.
A few other commands you might want to get familiar with include Grep, Find, and SSH.
These will help you locate specifically where the hacking took place on your site, so you manually remove the code that put you on the blocklist.
If the CLI stuff is leaving you scratching your head, here’s a list of resources you can use to get up to speed on the terminal and the specific commands you’ll need to clean your site:
- Command line
- Taming the Terminal
- How to Use cURL
- How to use grep command in Unix and Linux with examples
- How to Use Find from the Windows Command Prompt
Once you locate the source of the problem, you can remove it.
Or, if you’re a WPMU DEV member and have any questions about specific code and whether it’s an issue, contact our 24/7 support, and we’ll help you out.
Step 4: Removing Bad Code
If your site has been hacked, you’ll need to remove the malware that caused the blocklisting and/or security warnings.
If the hackers created new pages with malicious code, you could remove them from the SERPs altogether by going to the Search Console and using the Remove URLs feature.
You’ll also want to delete the pages in question from your server, but using Remove URLs can help expedite Google’s awareness of your cleanup attempt.
Again, I’ll refer back to Defender here as a simple solution. You can easily remove suspicious code in one-click with his help.
One thing to keep in mind is Defender does not scan the DB tables in cases where a Pharma hack has already happened. In this case, infected content on post pages needs to be cleared manually.
Remember, you shouldn’t use Remove URLs for pages you want to be indexed but have bad code. This is a feature you should only use when a page should disappear from search results for good.
To remove all evidence of your site’s hacking, you’ll need to backup from an older version of your site.
Regular backups are super important for this very reason, so hopefully, you have a clean version of your site on file to use. This is the first step in cleaning your site’s server.
Next, install any new core, theme, and plugin updates that are available. Make sure everything is as up to date as possible. This will reduce your site’s vulnerabilities.
Follow best practices for site security here (limit the number of plugins you use, delete outdated themes you no longer use, old user accounts, etc).
Finally, change all the passwords for your site. And I mean all of them. Not just the WordPress administrator and user passwords.
You also need to change the passwords for your FTP account, database(s), hosting, and anything else related to your site to ensure security.
If the version of the site you’re restoring from the backup is way out of date, you should make a disk image of your infected but current site before installing the clean outdated version.
Once you install updates and change passwords, you’ll need to restore the new content manually. Google offers some pointers on how to accomplish this.
Step 5: Resubmit Your Site
If your site has been blocklisted, it’s been removed from the search results. To get back in the SERPs, you’ll need to submit your site for review.
Otherwise, Google won’t know that you’ve taken steps to remedy the problem (or, at least, won’t crawl across your squeaky clean site for a long time).
And every day your site is out of the SERPs is money lost, right? So to speed things up, you have to go through a couple of official channels.
If your site was infected with malware or was involved in phishing, you’ll need to submit a reconsideration request via Google Search Console.
The steps required to submit a review depend on your specific security issue/situation, But luckily GSC has kindly outlined the full review and reconsideration process right here.
Once you’ve completed the review process, if Google finds your site is clean, warnings from browsers and search results should be removed within 72 hours.
You should also verify your site works as expected: pages load properly and links are clickable.
If your request is NOT approved, reassess your site for malware or spam, or for any modifications or new files created by the hacker.
Alternatively, you might consider requesting more help from specialists (WPMU DEV’s superhero support team is a great place to start!)
Have You Ever Been Hacked?
The process of cleaning up after being hacked and getting on Google’s blocklist can be arduous at best, I’m not going to lie.
But if you lay out a plan or create a checklist for the steps to take, you can tick them off little by little until your site is clean, back online, and back in the SERPs.
Plus, you can prevent hacking in the first place. Check out our article on stopping Hackers in their tracks with Defender.
It’ll take some effect, but the important thing is you’ll restore your site’s reputation.
And if anything, it’ll allow you to prioritize security in a way that you might not have thought about before.
Small silver lining?



Subscribe to MarketingSolution.
Receive web development discounts & web design tutorials.
Now! Lets GROW Together!